BLOG

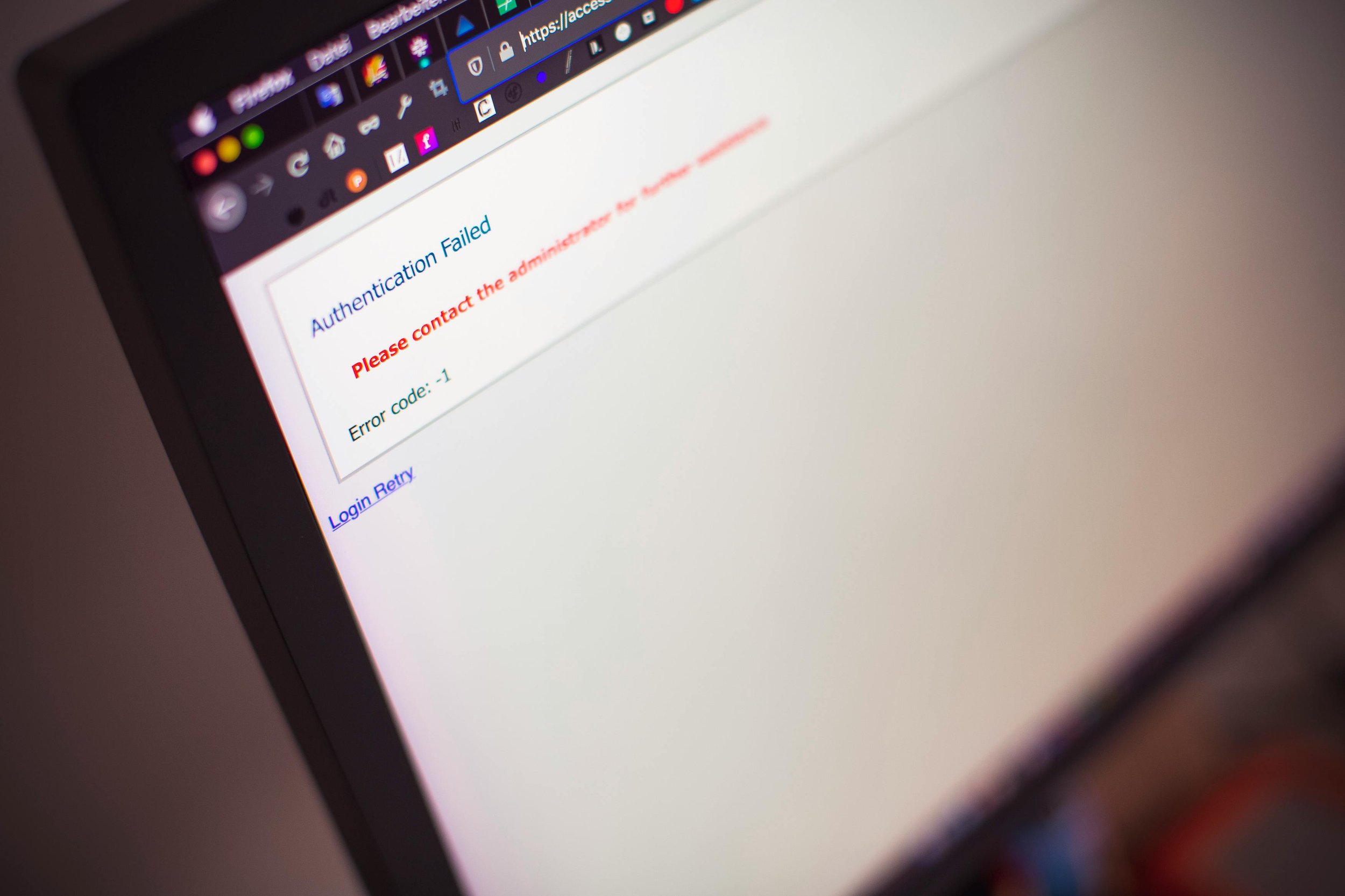
How to Prevent Ransomware Attacks in 2025
Ransomware attacks are evolving faster than ever, leveraging advanced tactics like AI-driven malware, double extortion, and supply chain vulnerabilities. In 2025, no business or individual is immune, making proactive cybersecurity measures essential.
What’s That Term: Microservices?
If you've spent any time in tech circles, you've probably heard the term "microservices" thrown around—especially when discussing modern software architecture. But what exactly does it mean? Microservices have revolutionized how applications are built, making them more scalable, flexible, and easier to maintain.

Why Penetration Testing is a Must for Cybersecurity
Cyber threats are more sophisticated and relentless than ever. Businesses, regardless of size, are prime targets for hackers looking to exploit vulnerabilities. While firewalls and antivirus software provide some level of protection, they are not foolproof.

The Future of IT Automation in Business Operations
IT automation is no longer a luxury—it’s a necessity for businesses looking to streamline operations, enhance security, and drive efficiency. From AI-powered workflows to self-healing IT systems, automation is transforming how companies manage their technology infrastructure. But what does the future hold?
IT Disaster Recovery Best Practices
IT disaster recovery is the cornerstone of business resilience, serving as a safeguard against the unexpected. At its core, it is a structured approach to restoring systems, data, and operations following an IT-related disruption.

What’s That Term: Data Fabric
In the ever-evolving world of technology, new buzzwords often emerge that promise to revolutionize the way we work with data. One such term making waves is "Data Fabric." But what exactly does it mean, and why is it becoming a cornerstone of modern data strategies?

The Power of Data Analytics in Decision-Making
Data analytics empowers leaders to move beyond guesswork, using insights drawn from patterns and trends to drive strategic choices. Whether optimizing operations, predicting market trends, or tailoring customer experiences, the power of data analytics in decision-making is transforming industries and redefining success.

Demystifying Zero Trust Architecture for SMBs
Small and medium-sized businesses (SMBs) face an ever-growing number of cybersecurity threats. With the rise of remote work, cloud adoption, and sophisticated hacking techniques, traditional security models are struggling to keep up.

The Risks of Shadow IT and How to Mitigate Them
In today’s fast-paced digital workplace, employees often turn to tools and software outside of their company’s approved technology stack to get their jobs done quickly and efficiently. While this practice—known as shadow IT—might seem harmless or even helpful in the short term, it introduces significant risks to organizational security, compliance, and efficiency.

What’s That Term?: Edge Computing
In today’s fast-paced digital world, technology continues to evolve, bringing us terms that seem straight out of science fiction—like "Edge Computing." But this concept is more than just a buzzword; it's a game-changer transforming how data is processed and utilized.
